Detecting Node-Hopping Attackers: Correlating Traces and Logs at Sub-Second Speed
Modern cyberattacks rarely stop at a single system. Once inside, attackers often move laterally, jumping between machines and services, in search of sensitive data or admin access. This tactic is known as node-hopping or lateral movement.
Detecting these attackers is not easy. Each step looks harmless in isolation. But when you connect logs and traces across systems, the pattern becomes clear. The key is doing it fast with real-time log correlation and sub-second detection speeds.
Node-hopping, a form of lateral movement, happens when:
In simple terms, it’s like a burglar sneaking room to room inside a building, rather than breaking directly into the vault.
Lateral movement detection is difficult because attackers:
This is why real-time threat detection is critical.
Logs record what happens inside each machine: logins, process starts, file access, and more. On their own, these entries can look normal. But when you correlate logs across multiple systems in real time, you start to see suspicious chains of activity that reveal lateral movement.
For example, you might find a pattern like:
Individually, none of these is alarming. Logins, remote connections, and admin commands all happen in normal operations. Together, they paint the picture of a node-hopping attacker.
Traces add another layer of visibility; many systems tag logs with session IDs or trace IDs. Traces essentially act as the thread that ties logs together into a clear attack path.
This makes it easier to follow an attacker’s path step by step, from one node to the next.. Without traces, you’d have to infer connections by timing, usernames, or IP addresses. With trace IDs, the link is explicit.
And if you correlate them (look at them together, in sequence, within a short time window), you realize this is suspicious:
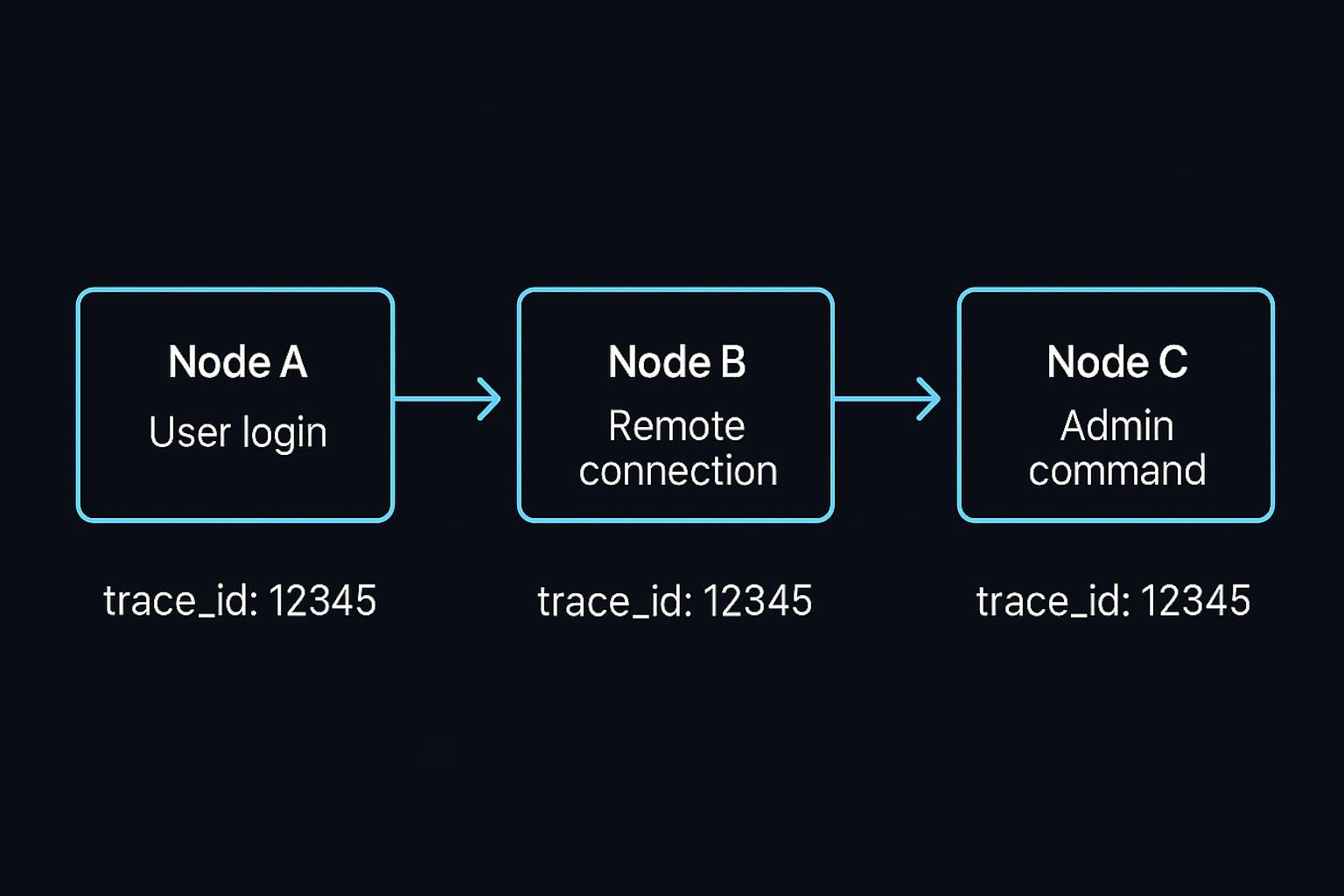
Logs are the raw events. But many systems also tag these logs with trace IDs (or session IDs).
This isn’t an after-the-fact investigation; it’s lateral movement detection in real time, giving defenders the speed to contain threats before they spread.
Now, let’s add speed into the picture. If your system can:
…then you can catch the attacker while they’re still moving.
That’s the difference between:
With logs + traces correlated in real time, you can:

Speed and visibility are the foundations of effective threat detection:
Attackers depend on slow, siloed systems. Real-time correlation turns the tables.
Different types of platforms support real-time log correlation and lateral movement detection:
Each of these plays a role in helping security teams gain speed and visibility, but they often come with trade-offs around cost, complexity, or data retention limits.
Node-hopping attackers thrive on blind spots and slow monitoring. Traditional methods miss the bigger picture because they analyze logs in isolation or too late.
The solution is real-time log and trace correlation at sub-second speed. By connecting events across systems instantly, you can expose lateral movement attacks in progress, not after the damage is done.
Speed plus visibility equals stronger defense. With the right tools and approach, defenders can catch node-hopping attackers in motion and shut them down before they reach critical targets.
At CtrlB, we believe, correlating logs and traces should not come at the cost of either speed or affordability. By pairing sub-second log search with trace-aware correlation directly from durable object storage, we help teams catch lateral movement even in historical data, without maintaining massive hot indexes or expensive SIEM stacks.
Join thousands of developers using CtrlB to monitor their systems with complete confidence and extreme precision.
Connect your entire stack in minutes with zero friction.
Sub-second latency on all queries. No waiting.
SOC2 Type II compliant, secure, and highly available.